Open source software carries risks that can stall or even derail M&A deals. Learn the pitfalls to watch for, how to navigate the technical due diligence process, and ways to mitigate software risk effectively. The result is faster, safer deal execution and stronger long-term value.
The Reward and Risk of OSS
There’s little question today about the value of open source software (OSS). The preexisting, proven, and free components spur innovation, speed up time to market, and come with a wealth of developer experience and expertise.
As usage continues to climb—OSS now comprises 80% of all proprietary applications—it’s hard to overstate the value. Globally, companies would need to spend an estimated $8.8 trillion to recreate the open source software they now rely on, according to a working paper from Harvard Business School, “The Value of Open Source Software.”
While OSS usage is mission-critical for most organizations, it also comes with responsibilities and risks. While anyone can see and download OSS code for free, one common mistake is to equate OSS with “free software.” Finding code on the internet that suits your purposes doesn’t mean you have permission to use it. Most OSS is released under a license and requires a contractual relationship. Some licenses are extremely permissive, while others are much more restrictive.
In the context of a transaction, such as IPOs, loan applications, financing, divestitures, and specifically, mergers or acquisitions (M&A), the risks become much higher. Software is a key component of most M&A deals, and all parties should expect a complete picture before a successful transaction can be completed
Unfortunately, in an M&A, OSS risk issues are sometimes overlooked, often not well understood, and almost always addressed much later than they should be.
5 Ways OSS Risk Applies to M&A
How might OSS usage impact an M&A? Here are five of the most common issues.
- Licensing and compliance liabilities
Inappropriate code use or attribution failures are examples of how OSS may be misused, according to licensing terms. In these instances, you could be considered in breach of your contract with the software developer and accused of copyright infringement. Your entire program may be at risk of being viewed as a derivative of the OSS, which could force you to either release the entire program that uses the source code or pay a significant price for not doing so. The risk of having to turn over source code or paying to avoid a handover may impact valuation or, because the buyer could ultimately be buying a lawsuit, cause the entire transaction to fail.
- Security vulnerabilities
Like commercial software, security vulnerabilities also impact OSS. Cyber criminals are known to inject malicious code into openly published libraries, and if you’re unclear on what’s in your code, you may not notice an issue until it’s too late, and the exploit has already done its damage. You can’t launch defenses against risk you can’t see, and, in an M&A, that risk could get passed on to the buyer.
- Business and operational risk
If you use, modify, or distribute software covered by a copyleft license, you are required to make your modified version available under the same license. Often, such disclosures are the responsibility of one person, and in an M&A, it’s easy to lose this knowledge and expertise, which could result in compliance failure.
A failure to shut down abandoned projects, if they use OSS, could become both compliance and security issues because they aren’t monitored or maintained.
- Remediation costs
After a close review of your OSS and third-party components, you will probably also have a list of necessary remediation actions. This might include legal issues, securing licenses, code remediation needs that may involve removal and replacement, and a notice and attribution to-do list, which is required for compliance. These costs could impact valuation.
- Recent enforcement and litigation
Vendors that release both OSS and commercial versions of code (known as dual licensing modes) are often selective about enforcement. They may not accuse a start-up of misuse, but unfortunately, once the calculus changes with the introduction of deeper pockets in an M&A, they may change their tune. Litigation is highly costly.
Other transaction-related risks to consider
There are other risks worth considering ahead of a transaction. Greater brand visibility can invite increased scrutiny and risk. So can changes in the distribution model after a sale. The brain drain that inevitably occurs when developers come and go is also standard.
Even if M&A isn’t in your immediate plans, these software risks can and should be addressed now.
The more proactive a company is about software ahead of a potential transaction, the quicker an agreement can be drafted and closed with confidence, to the satisfaction of both buyer and seller.
SBOMs
As you walk through a technical due diligence process, you will inevitably create a Software Bill of Materials (SBOM). A precise inventory of the components in your code, a SBOM offers critical, timely intelligence for software producers and users, as well as buyers and sellers.
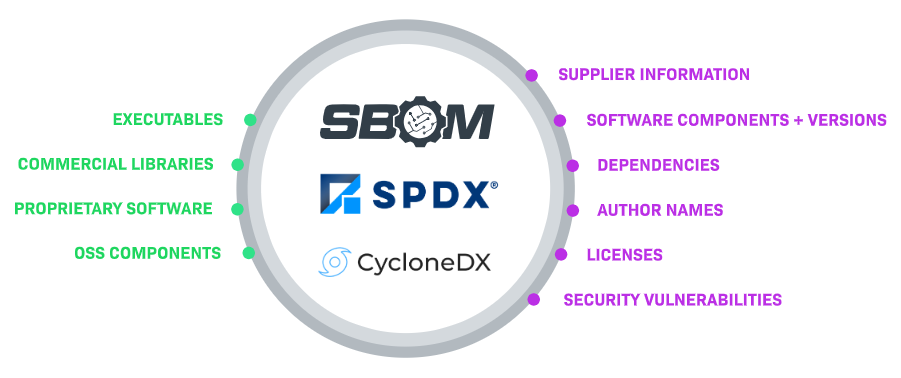
An SBOM is complete, machine-readable code documentation. The queryable record includes details from multiple sources about a software application’s connected components, versions, and dependencies. It accounts for all the commercial libraries, proprietary software, open source dependencies, and information on the suppliers and code authors. Ideally, licensing information and security vulnerability reports are also included.
With this complete list of components, buyers and sellers can better understand the software supply chain and manage organizational risk accordingly.
Ready for diligence? Use this best practices checklist
Checklist
- Create OSS policies.
Create a succinct OSS policy or policies specific to your organization’s goals, culture, and strategies that govern your use of OSS. - Define and implement processes.
Outline your organization’s processes for OSS use. Include the rules for what may and may not be used, along with repercussions. - Create a third-party software inventory.
Compile a list of OSS and third-party commercial software to provide a complete picture of your risk posture. - Maintain up-to-date notice and attribution files.
Maintain license text, copyright notices, and attribution statements so they may be easily shared. - Track OSS contributions.
Implement a process that captures documentation on OSS contributions and provide that information during an M&A.
By following these best practices, you will be well-prepared to effectively negotiate who bears the risk, ensuring both buyers and sellers receive the best value for their investment.
OSS Management: How Revenera SCA Solutions Help
Managing growing application portfolios and an increasing reliance on OSS can’t be purely manual. A strong toolset is required.
SCA tools from Revenera help you discover, assess, and manage license and security risk across all software applications. Learn more about how we support the construction of complete, accurate SBOMs, manage legal and security risk, and deliver compliance artifacts for comprehensive OSS management and in preparation for an M&A.
Manage complex SBOMs
Revenera SBOM Insights will collect and ingest SBOM parts from multiple sources to create an SBOM in a SaaS environment, aggregate that data into a single repository, and provide full visibility for security, legal, downstream supply chain partners, and transaction partners. Ensure your risk reports for license compliance and security risks are up-to-date and ready quick response when necessary, and a technical diligence review.
Comply with third-party notice requirements and identify security vulnerabilities
Code Insight is a single integrated solution for open source license compliance and security. Find vulnerabilities and remediate associated OSS risk during the build process and throughout their lifecycle. Implement a formal OSS strategy that balances business benefits and risk management, and manage open source license compliance, including compiling third-party notices, to ensure
your diligence review proceeds smoothly.
Frequently Asked Questions (FAQs)
OSS risk in M&A refers to legal, security, and operational issues that arise from the use of open source software in acquired applications. These risks can include license violations, undisclosed vulnerabilities, and remediation costs. If not addressed early, they can delay or derail transactions.
Software is often a core asset in modern M&A deals, and OSS usage directly impacts its value and risk profile. Undocumented components or license obligations can reduce valuation or introduce legal exposure. Buyers need full visibility before completing a transaction.
The most common compliance risks include improper license use, missing attribution, and failure to disclose copyleft obligations. These issues can force code disclosure or trigger legal action. During M&A, these risks often surface late and cause delays.
Security vulnerabilities in OSS can be inherited by the buyer after acquisition. Without a full inventory, exploits may go unnoticed until after the deal closes. This increases post-acquisition remediation costs and operational risk.
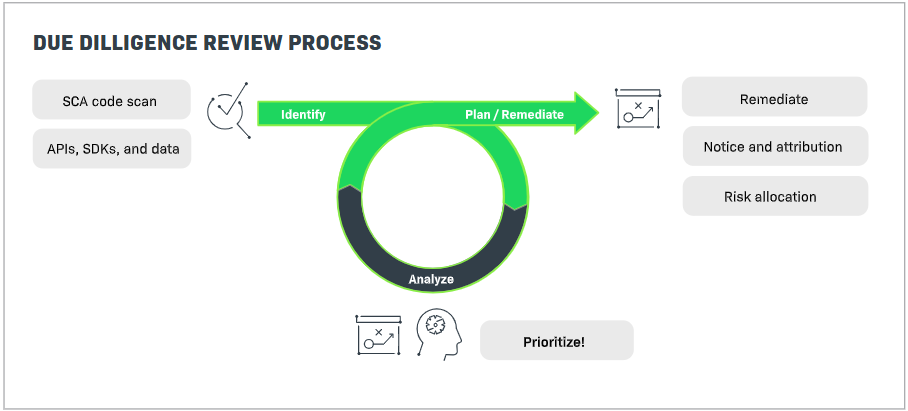
Technical due diligence evaluates the software assets involved in a transaction, including OSS usage, licenses, and security posture. It provides buyers with clarity on what they are acquiring. Sellers benefit by reducing surprises and accelerating deal timelines.
An SBOM is a detailed inventory of all software components and dependencies. In M&A, it provides transparency into the software supply chain. This helps buyers assess risk and sellers demonstrate compliance readiness.
Remediation efforts may require replacing components, securing licenses, or addressing legal issues. These actions can increase costs and reduce valuation. Identifying remediation needs early allows for informed negotiations.
Copyleft licenses may require modified source code to be disclosed under the same license. In M&A, this can impact intellectual property value. Understanding how OSS is used is critical to managing this risk.
OSS risk should be addressed well before any transaction is planned. Proactive governance shortens due diligence timelines and builds buyer confidence. Waiting until a deal is underway often leads to delays
Companies should maintain an accurate OSS inventory, enforce policies, and generate SBOMs. Using automated SCA tools helps ensure accuracy. Preparation enables smoother negotiations and faster deal closure.
Resources
Webinar
Regulations Roundup: Navigating SBOM and OSS Compliance Across the US, India, and Europe
Join us for a comprehensive “regulations roundup” that brings together perspectives from multiple regions, clarifies what’s mandated now, and offers practical advice for staying compliant and competitive in a global market.
Webinar
How to Manage Open Source Risk in M&A
In this webinar, we'll explain the issues, provide ways to mitigate risk and break down why being proactive is critical. Don't wait until a deal is on the table to find out you have a problem. Register to learn more.
eBook
Open Source Software Risk in M&A
Open source risks can derail M&A deals. Read the whitepaper to learn pitfalls, due diligence steps, and ways to mitigate software risk.
Webinar
The Supply Chain Risk You Can’t Ignore: A Playbook for Critical Industries
The webinar will benefit development leads, CIOs, and CTOs responsible for navigating compliance and mitigating supply chain risks. Don’t miss out to gain actionable insights for protecting your organization in an increasingly complex environment
White Paper
Risky OSS: How Regulated Industries Can Secure the Software Supply Chain
This whitepaper reviews the state of OSS, four management use cases, and best practices and solutions to help security and legal teams in highly regulated industries. Access now to learn how you can confidently mitigate rising supply chain risk.
Data Sheet
OSS Inspector Plugin
Ensure your code is secure and compliant by effortlessly managing open source dependencies directly in your IDE.
Want to learn more?
See how Revenera's end-to-end solution delivers a complete, accurate SBOM while managing license compliance and security.