Software activation typically requires an internet connection but in some cases that’s simply not possible. Here’s how you can handle software activation in disconnected environments.
Despite the rapid growth of interconnectivity among software and devices (think Internet of Things) there are still many instances where products operate in environments without network connectivity (aka disconnected environments or dark sites).
Unfortunately many software producers and device manufacturers struggle when working with electronic software delivery to activate and update their products in environments with little to no connectivity which leaves them exposed to piracy and non-compliance.
What’s at Risk?
Even if your software products can’t “call home” you still need a way to activate them. After all, activation is the check-point for your products to call home from the field so that you can validate the software and ensure that your customer has paid for rights to use the software. This helps minimize software piracy and ensures that your customers are in compliance with your EULA (end-user software licensing agreement) and you’re not giving-away your precious IP.
Types of Disconnected Environments
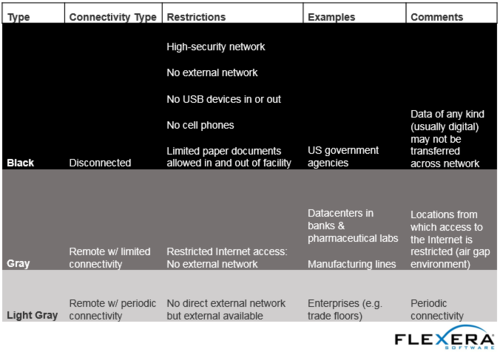
There are several types of disconnected environments you should keep in mind, as each carries its own unique characteristics that should be considered when designing your software activation process. Let’s explore some examples:
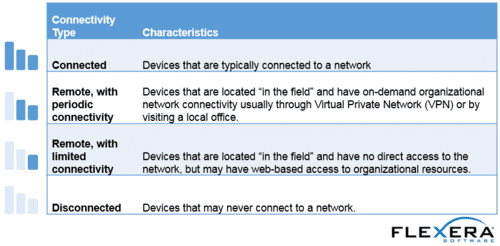
Shades of Darkness
In addition to the types of disconnected environments, there are a few shades of darkness which means that you’ll need different activation strategies depending on how dark the operating environment is:
Activation Options in Disconnected Environments
While there are several types of disconnected environments, we’ll focus on black sites where there is no connectivity available. If you’re an application producer that requires support in such an environment, you should consider alternative options to product activation.
Keyboard-only activation can help when there is no digital exchange between the isolated network and the outside world – the only input device may be a keyboard. This model involves exchanging machine fingerprint information and activation keys over a non-digital media (e.g. paper), so that the end user can still activate the software.
By making sure you can activate your products in disconnected environments you can rest assured that you’re minimizing the risk of your software being pirated and that your customers are in compliance.