The recent botnets, involving networked security cameras, shone a light on the vulnerability concerns around Industrial Systems and the Industrial IoT (IIoT).
These types of devices have characteristics that make them a compelling target for botnet authors, as well as other types of malware. They typically have full-time, high-speed network connections, run embedded Linux, and lack monitoring systems and screens or logs that might alert a user to a hack. Additionally, many of these systems are designed for limited roll-out, or come from a company who has paid limited attention to hardening or security. This combination of powerful networked systems, with easy ability to be breached, allows for botnets to thrive. In the last few years, malware such as Mirai and Bashlite, have taken advantage of vulnerabilities in IoT devices, and these weaknesses should be kept in mind as the industry designs the next-generation of IoT and IIoT devices.
The typical embedded Linux system uses dozens to hundreds of open source packages. While these components are typically high quality, all software contains defects. Over time vulnerabilities in these components are discovered and eventually taken advantage of. Still, many devices are not designed to be auto-updated, and depend on software from commercial and open source organizations that have vulnerabilities discovered every few weeks to every few months.
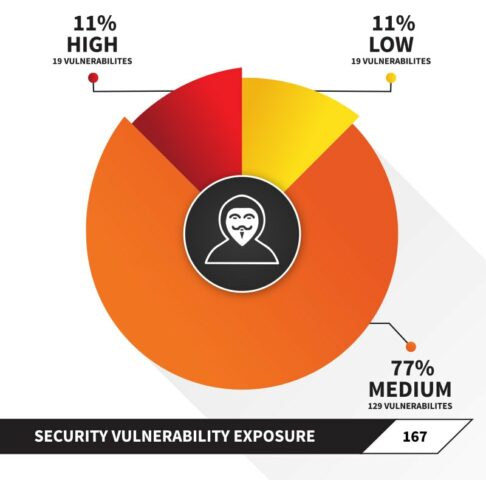
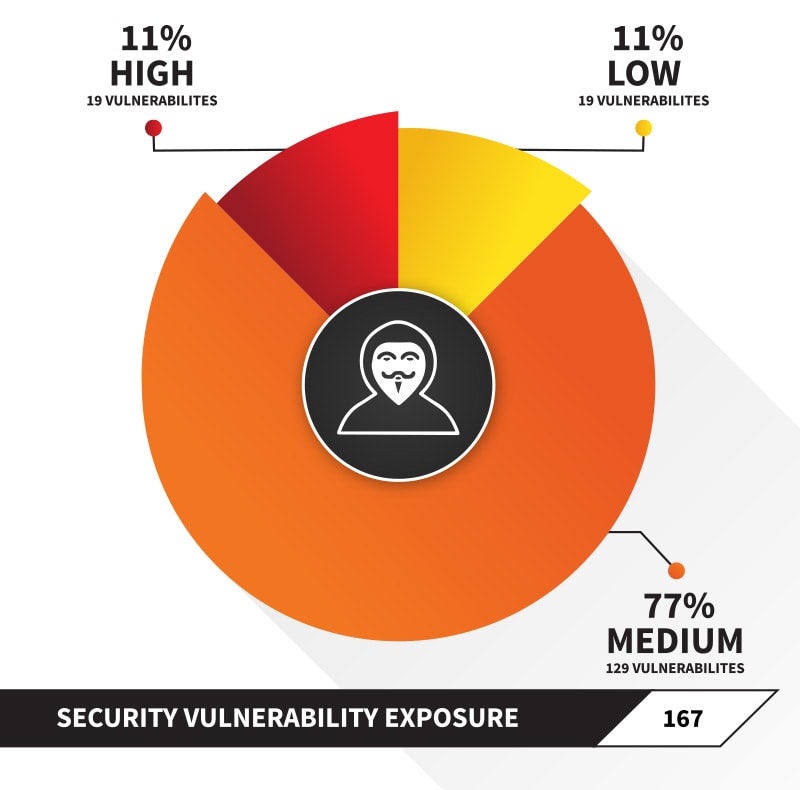
It is becoming a best practice to pay attention to a device’s Software Bill of Materials, with special attention to components with known vulnerabilities as seen in places such as the National Vulnerability Database. By keeping track of the list of components used in the operating system as well as the application itself, a company can stay ahead of malware authors – especially if they have a rigorous patching system in place.
Software Composition Analysis contains scanning and workflow features designed to help technology companies discover, manage, upgrade and comply with their use of open source components. By scanning and comparing the files used on the devices to a database of billions of known open source files, you are able able to discover usage of third-party components for the purposes of vulnerability management as well as open source license compliance. Managing these requirements allows a developer to ship a device that respects the open-source community, as well as protects the company’s users from attacks.